Protecting the Infrastructure That Powers the World
Advanced hardware-based cybersecurity for high-risk environments.
Advanced hardware-based cybersecurity for high-risk environments.
From defense to energy and advanced manufacturing, Allpriv protects high-risk environments with hardware-enforced security.

Modern military drones operate in hostile environments where interception, spoofing, and remote takeover are constant threats.
Hijacking, GPS spoofing, signal jamming and data interception.
Solar farms and wind power installations are highly connected — often easy targets with multiple entry points for cyberattacks.
Remote control system manipulation, SCADA attacks, grid disruption, energy production sabotage, and exploitation of unsecured access points.
Allpriv secures hardware endpoints across inverters, control systems, sensors, and remote monitoring terminals — closing entry points and preventing attackers from bypassing software defenses.

Oil refineries, offshore platforms, and energy grids are prime cyber targets. Each facility operates with thousands of connected devices — sensors, controllers, terminals, and embedded systems — creating thousands of potential entry points for cyberattacks.
Control system manipulation, SCADA attacks, operational disruption, and strategic data theft.
Allpriv secures hardware endpoints across control systems, sensors, and remote terminals — blocking attackers from bypassing software defenses.

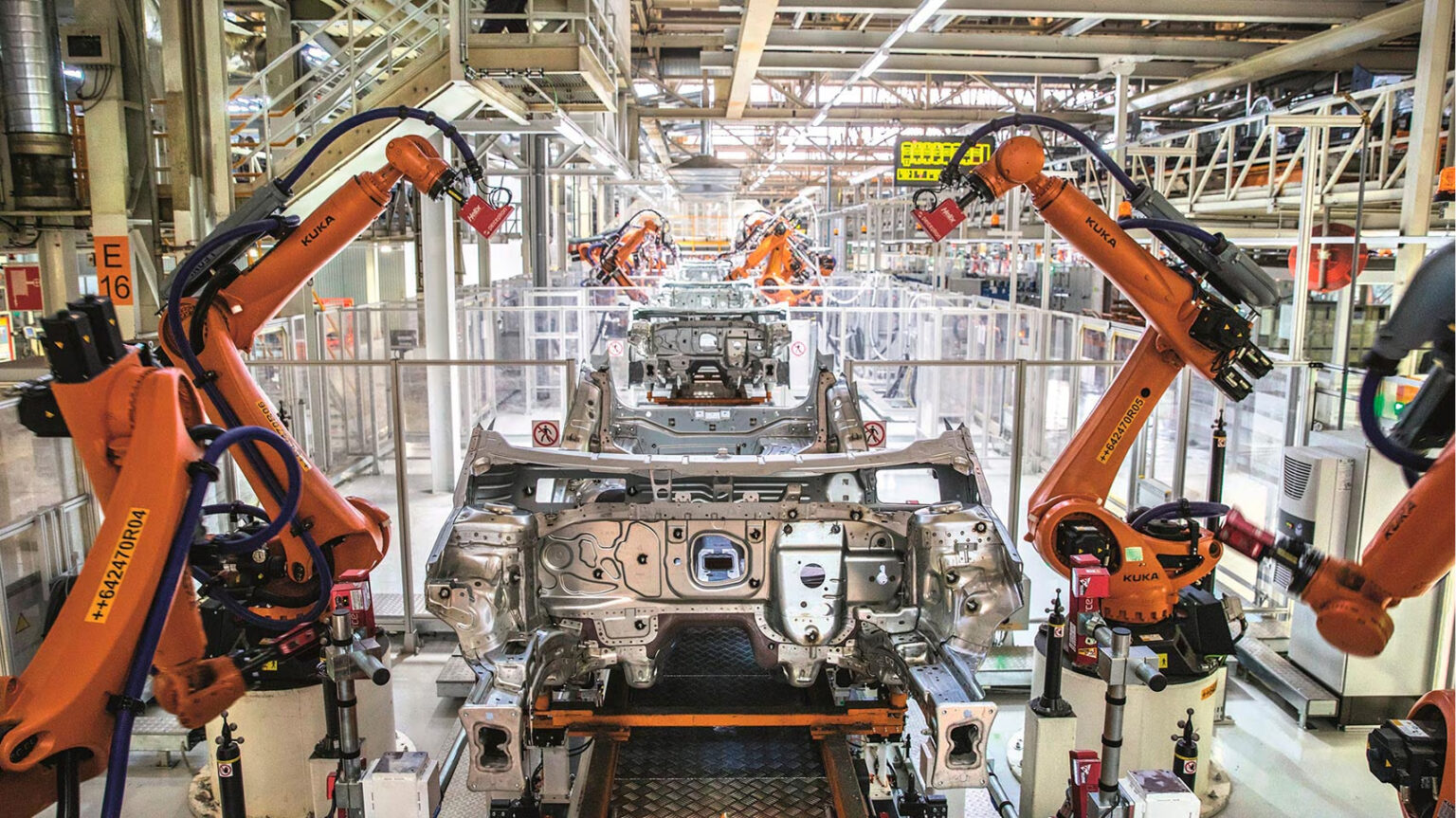
Much of this infrastructure is legacy technology — expensive, long-lifecycle equipment that cannot be replaced or upgraded every few years. These outdated systems often lack modern cybersecurity protections, creating persistent vulnerabilities.
Ransomware, system sabotage, PLC manipulation, costly downtime, and industrial espionage.
Allpriv secures hardware endpoints and machine interfaces — protecting control systems, IoT gateways, and embedded devices from unauthorized access.
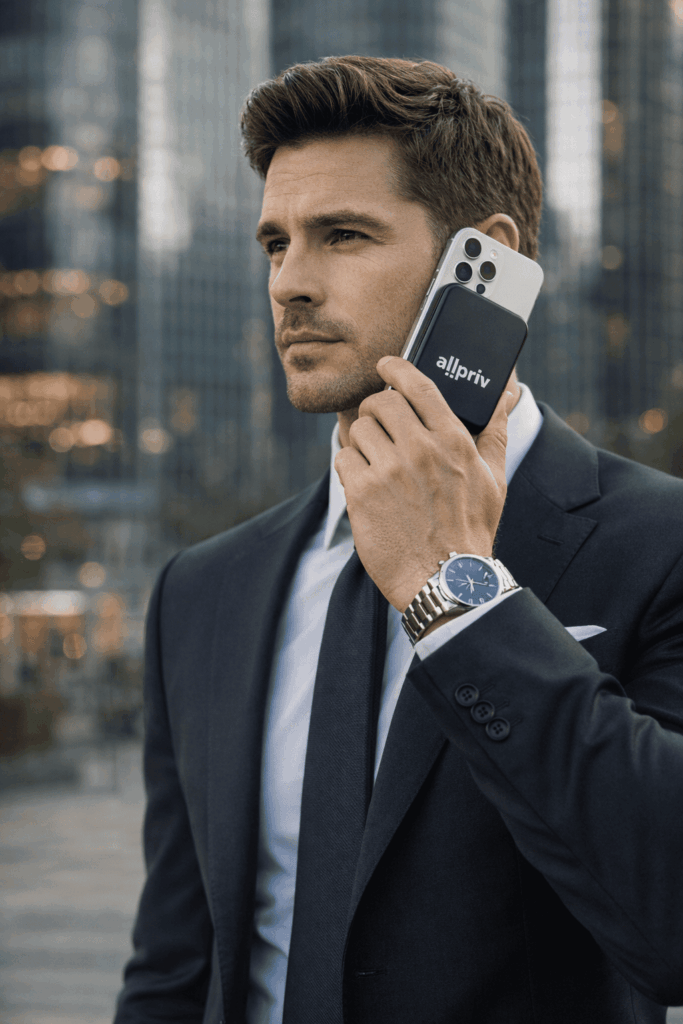
Military-grade secure communications mobile devices are essential when discretion and operational security are critical.
Location tracking, IMSI catchers, metadata monitoring, unauthorized access — and communications hacks that remain undetected.
Allpriv secures mobile devices at the hardware level, delivering military-grade protection.
No phone number. No tracking.
No remote intrusion. No communication compromise.
Allpriv is a company specializing in cybersecurity, we want to simplify and centralize the means of protection against external attacks.

